CST Cybersecurity Regulatory Framework (CRF): Complete Compliance Guide for Saudi ICT Providers

The CST CRF (Cybersecurity Regulatory Framework) is a mandatory cybersecurity compliance framework issued by Saudi Arabia’s Communications, Space & Technology Commission (CST), formerly CITC. It applies to all organizations licensed or registered by CST in the ICT, telecom, and postal sectors. The framework defines 215 controls across 6 domains, organized into 3 compliance levels (CL1, CL2, CL3). The current version is Version 2, issued in October 2023.
If your organization holds a license or registration with Saudi Arabia’s Communications, Space & Technology Commission (CST) — whether as a telecom operator, ISP, IT service provider, or postal company — the CST Cybersecurity Regulatory Framework (CRF) is not optional reading. It is a mandatory regulatory requirement that directly affects your ability to operate in the Kingdom.
Originally issued in June 2020 and updated to Version 2 in October 2023, the CRF defines the minimum cybersecurity maturity that licensed ICT service providers must demonstrate, verified through self-assessments, field inspections, and CST audits. This guide breaks down everything you need to know: who the CRF covers, its six control domains, how its three compliance levels work, and what GHS does to get Saudi ICT organizations to full compliance efficiently.
Oct 2023
CL1 · CL2 · CL3
What Is the CST Cybersecurity Regulatory Framework (CRF)?
The CRF is a comprehensive set of cybersecurity requirements established by the Communications, Space & Technology Commission (CST) — the regulatory body that governs Saudi Arabia’s telecommunications, ICT, and postal sectors. Its primary objective is to increase the cybersecurity maturity of Saudi ICT service providers in a structured, measurable, and risk-proportionate way.
The framework was developed in coordination with the National Cybersecurity Authority (NCA) and aligns closely with international standards including ISO 27001, ISO 27002, and the NIST Cybersecurity Framework. This means organizations pursuing CRF compliance also make significant progress toward satisfying international security audits and client expectations — making compliance a multiplier, not just a tick-box.
A key principle of the CRF is its risk-based approach: rather than imposing a single uniform standard on all ICT providers, the framework assigns different compliance obligations based on each organization’s size, services, risk profile, and infrastructure complexity. This is operationalized through the three compliance levels described below.
Who Must Comply with the CST CRF?
The CRF applies to all organizations licensed or registered by CST in Saudi Arabia’s ICT, telecommunications, and postal sectors — and extends to their subsidiaries, staff, third-party contractors, and customers. This includes:
| Organization Type | CRF Applies? | Notes |
|---|---|---|
| Telecom operators & ISPs | ✅ Mandatory | Core target of the framework |
| IT service providers (licensed by CST) | ✅ Mandatory | Includes managed services, cloud, hosting |
| Postal service providers | ✅ Mandatory | Licensed by CST |
| Subsidiaries of the above | ✅ Mandatory | Obligation flows through parent entity |
| Third-party contractors & vendors | ⚠️ Indirect | Subject to Third-Party Security domain requirements |
| Critical National Infrastructure (CNI) entities | ⚠️ NCA ECC primary | CNIs follow NCA ECC; CRF may also apply — see below |
One important distinction: organizations classified as Critical National Infrastructure (CNI) fall primarily under the NCA Essential Cybersecurity Controls (ECC) rather than the CRF. However, depending on their CST licensing status, they may be subject to both frameworks simultaneously. If you are unsure which framework applies to your organization, a gap assessment is the fastest way to clarify.
The 6 Control Domains of the CST CRF
The CRF organizes all 215 cybersecurity controls across six main domains. Each domain addresses a distinct area of cybersecurity risk and is subdivided into more specialized sub-domains with specific, measurable controls assigned across CL1, CL2, and CL3.
Governance
Cybersecurity strategy, policy development, roles and responsibilities, awareness and training programs, and senior management accountability. Establishes the organizational foundation for all other domains.
Asset Management
Inventory, classification, and lifecycle management of all ICT assets — hardware, software, data, and services. Ensures organizations know what they own and can protect it accordingly.
Cybersecurity Risk Management
Risk identification, assessment, treatment, and monitoring. Includes business continuity planning, incident response, and ensuring cybersecurity risks are formally integrated into organizational decision-making.
Logical Security
The most granular domain. Covers access control, network segmentation, vulnerability management, secure software development, cryptography, logging, monitoring, and protection against advanced threats. Applies the broadest set of technical controls.
Physical Security
Protection of physical premises, data centers, server rooms, and hardware assets. Covers access controls for physical facilities, environmental protections, and equipment management procedures.
Third-Party Security
Managing cybersecurity risks introduced through vendors, outsourced services, and supply chain relationships. Includes due diligence, contractual security requirements, ongoing monitoring, and screening of contractor personnel.
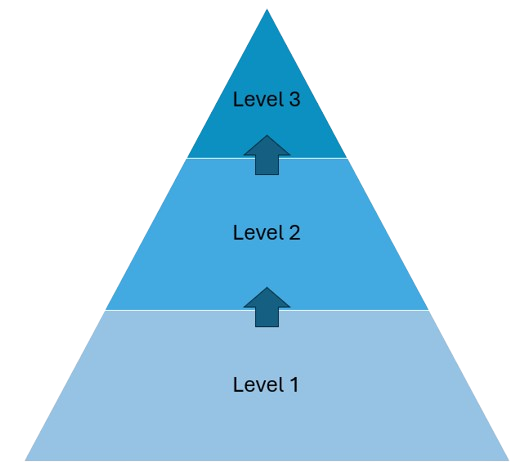
The 3 Compliance Levels: CL1, CL2, and CL3
The CST CRF adopts a tiered, risk-based structure. Each organization is assigned a target compliance level (CL1, CL2, or CL3) by CST based on its individual risk profile. Higher compliance levels require full achievement of all preceding levels first — there is no skipping ahead.
Compliance Level 1 — Basic Security Controls
The entry-level compliance tier, establishing foundational cybersecurity practices. CL1 covers essential governance structures, basic asset inventories, fundamental access controls, perimeter security, and minimum incident response capability. This is the mandatory minimum for all in-scope organizations.
Compliance Level 2 — Advanced Requirements
Builds on CL1 with more sophisticated controls. CL2 adds requirements for formal risk management programs, advanced threat detection, third-party auditing, encryption standards, secure development practices, and stronger network monitoring. Assigned to organizations with greater complexity or higher risk profiles.
Compliance Level 3 — Efficiency Monitoring & Continuous Improvement
The highest tier. CL3 focuses on measuring the effectiveness of all CL1 and CL2 controls, continuously optimizing security practices, and demonstrating measurable improvement over time. This level is required for larger, higher-risk ICT service providers and reflects a proactive, continuously improving security posture.
How CST Determines Your Required Compliance Level
The compliance level assigned to your organization is not self-selected — it is determined by CST through a formal process:
- 1️⃣ Submit the classification form: Complete the “Determine Service Provider Level to Specify Required Level of Compliance” form and submit it to CST via CRF@citc.gov.sa within 5 working days of the framework entering into force for your organization.
- 2️⃣ CST notifies your target level: Within 15 working days, CST communicates your required compliance level (CL1, CL2, or CL3) based on your size, services, number of employees, and ICT infrastructure complexity.
- 3️⃣ Submit a self-assessment: Complete and submit the “Self-Assessment Form to Measure Current Reality of Cyber Security Maturity Level” to CST within 3 months, documenting your current cybersecurity posture against the CRF controls.
- 4️⃣ Implement and report: Submit periodic compliance progress reports to CST as required. CST monitors compliance through self-commitment models, field inspections, compliance workshops, and proactive or incident-triggered audits.
Need to Determine Your CRF Compliance Level?
GHS runs a rapid CRF gap assessment that benchmarks your current cybersecurity posture against your target compliance level, identifies every control gap, and gives you a prioritized remediation roadmap — before CST audits do.
Get a Free CRF Assessment →CST CRF vs. NCA ECC: Understanding the Difference
Saudi Arabia has multiple cybersecurity frameworks that sometimes overlap. The two most commonly confused are the CST CRF and the NCA ECC. Here is how they differ:
| Dimension | CST CRF | NCA ECC |
|---|---|---|
| Issuing body | Communications, Space & Technology Commission (CST) | National Cybersecurity Authority (NCA) |
| Primary scope | ICT, telecom, and postal service providers licensed by CST | All government & private sector organizations; mandatory for CNIs |
| CNI applicability | Excludes most CNIs (they follow ECC instead) | Primarily targets CNIs and government entities |
| Structure | 6 domains, 215 controls, 3 compliance levels (CL1–CL3) | 5 domains, ~114 controls, single compliance standard |
| Alignment | ISO 27001, ISO 27002, NIST CSF, NCA ECC | ISO 27001, NIST CSF, IEC 62443 |
| Overlap possible? | Yes — some organizations must comply with both, particularly larger ICT providers that also manage critical infrastructure. | |
The CRF also aligns with and complements SAMA CSF (for financial institutions), PDPL (Saudi data protection law), and Aramco CCC — making a well-implemented CRF program a strong foundation for satisfying multiple regulatory obligations simultaneously.
Why CRF Compliance Matters Beyond the Regulatory Obligation
CRF compliance is often initially viewed as a regulatory burden. In practice, organizations that achieve and maintain compliance gain tangible business advantages:
- 🔑 License continuity: Non-compliance puts your CST license at risk. CST conducts field inspections and audits, and has the authority to issue non-compliance findings that affect your operating status.
- 🏆 Competitive advantage: Demonstrated compliance builds trust with government and enterprise clients who increasingly require evidence of cybersecurity maturity from their ICT suppliers.
- 📜 Multi-framework efficiency: CRF controls overlap significantly with ISO 27001, NCA ECC, and SAMA CSF, so compliance work done for the CRF contributes directly to satisfying other frameworks.
- 🛡️ Genuine risk reduction: The six control domains address real-world attack vectors. Organizations that implement CRF controls properly see measurable reductions in vulnerability exposure, incident frequency, and breach impact.
- 🌍 Vision 2030 alignment: Saudi Arabia’s digital transformation agenda requires a secure, trusted ICT ecosystem. CRF compliance positions your organization as a trusted participant in that ecosystem.
How GHS Helps Saudi ICT Providers Achieve CST CRF Compliance
At GHS (Gray Hat Security), our certified team — CISSP, CISM, and OSCP — has guided Saudi ICT organizations through CST CRF compliance across all three levels. We understand both the technical requirements of the framework and the operational realities of businesses working under CST regulatory oversight.
CRF Gap Assessment & Compliance Level Mapping
We benchmark your current cybersecurity posture against all 215 CRF controls, mapped to your assigned compliance level (CL1, CL2, or CL3). You receive a clear gap report showing exactly which controls are missing, partially implemented, or fully compliant — with risk prioritization and a realistic timeline to full compliance.
Policy & Documentation Development
We develop all required documentation for CRF compliance — cybersecurity strategies, risk management frameworks, asset management policies, incident response plans, access control procedures, change management processes, and awareness and training materials — all aligned to the CRF control language and CST expectations.
Technical Controls Implementation
We implement the technical controls your organization is missing — network segmentation, identity and access management, endpoint detection and response (EDR), data loss prevention (DLP), logging and monitoring solutions, vulnerability management programs, and secure configuration baselines. We don’t just advise; we deploy.
Self-Assessment Support & CST Submission
We prepare your self-assessment submission to CST, compile your compliance evidence portfolio, and conduct internal mock assessments before any CST field inspection. Our team stays available throughout the assessment process to address any queries or findings raised by CST.
Ongoing Compliance Monitoring
CRF compliance is not a one-time exercise — CST requires periodic reporting and continuous maintenance of controls. GHS provides ongoing monitoring, periodic review cycles, and update support whenever the CRF is revised, ensuring your compliance never lapses.
Frequently Asked Questions
The CST CRF is a foundational regulatory requirement for every ICT, telecom, and postal service provider operating under a CST license in Saudi Arabia. With 215 controls spread across six domains at three compliance levels, it demands a structured, documented, and auditable cybersecurity program — not informal practices. The organizations that invest in proper CRF compliance don’t just satisfy CST: they build the cybersecurity maturity that protects their operations, enables their growth, and earns the trust of government and enterprise clients in the Kingdom.
Ready to Achieve CST CRF Compliance?
GHS provides end-to-end CRF compliance support — from gap assessment and policy development to technical implementation, self-assessment submission, and ongoing monitoring. Let’s start with a free readiness review.
Talk to a GHS Expert →Reference: CST Cybersecurity Regulatory Framework — Official Document (cst.gov.sa)